Legal Data in the Cloud: How Lawyers Accidentally Waive Attorney-Client Privilege Using Everyday Tools
The Assumption Behind Modern Legal Work
There is a quiet assumption built into modern legal workflows: If you are using widely adopted tools—email, cloud storage, shared drives—they must be secure enough for professional use.
Most of the time, nothing appears to go wrong. Files move seamlessly between parties. Drafts are shared, reviewed, and revised. Clients are served efficiently. The system feels stable.
But that stability is deceptive.
These tools are not designed for adversarial environments. They are designed for collaboration. And in legal practice, that difference matters.
The failure mode is not loud. It does not look like a breach or an attack. It looks like normal usage…until the consequences become irreversible.
When Convenience Overrides Containment
Modern cloud systems prioritize ease of use:
- Links are easy to generate and distribute
- Files sync automatically across devices
- Permissions are flexible and often persistent
- Data is stored on infrastructure outside your direct control
From a product perspective, these are advantages.
From a legal perspective, they introduce silent points of failure.
The core issue is not misuse—it is misalignment.
Legal work assumes:
- restricted access
- controlled distribution
- clear ownership boundaries
Cloud systems assume:
- sharing
- accessibility
- fluid collaboration
When these assumptions collide, the risk is not hypothetical. It is structural.
Case Study: When a Link Becomes a Legal Liability
In Harleysville Insurance Co. v. Holding Funeral Home, Inc., a law firm uploaded case-related documents to what they believed was a controlled environment. The files were accessible through a public-facing link. Opposing counsel found them.
There was no hacking involved. No intrusion. No system failure in the traditional sense.
The system functioned exactly as designed: it allowed access. The court ruled that this disclosure waived attorney-client privilege.
That outcome carries significant implications:
- Protected legal strategy became accessible to the opposing side
- Confidential communications were no longer shielded
- The privilege, once lost, could not be restored
This is the critical point:
Privilege is not partially waived. It is either intact—or gone. And in this case, it was gone because of a link.
Case Study: Systemic Exposure at Scale
In J-M Manufacturing Co. v. McDermott Will & Emery, the issue was not a single document or misconfigured link.
It was the broader handling of electronic data across systems.
Confidential materials were exposed at scale, leading to hundreds of millions of dollars in malpractice claims.
The failure did not originate from a single catastrophic event.
Instead, it emerged from:
- routine document handling practices
- distributed data storage
- insufficient control over digital access points
This is what makes modern data risk difficult to detect: It accumulates gradually. Each individual action appears reasonable. Each system behaves as expected. But collectively, they create conditions where sensitive information can move beyond control.
Why Legal Data Exposure Happens Without a Breach
Traditional thinking associates risk with external threats—hackers, attacks, unauthorized access. But in many legal cases, exposure occurs without any malicious actor. The system itself enables it.
Examples include:
- Public or semi-public sharing links
- Auto-synced folders across multiple devices
- Misconfigured permissions inherited across teams
- Third-party platforms storing and replicating data
These are not edge cases. They are default behaviors in many cloud environments. And critically, they operate without friction. That means risk is introduced quietly—and often invisibly.
How AI Tools Introduce a New Layer of Risk to Legal Confidentiality
The introduction of cloud-based AI tools changes the nature of data handling entirely. You are no longer just storing information. You are actively processing it outside your environment.
When legal professionals input data into AI systems, that data may include:
- client facts
- draft arguments
- internal strategy notes
- sensitive communications
Depending on the platform, this interaction can result in:
- temporary or persistent data retention
- logging for system monitoring or improvement
- storage across distributed infrastructure
- unclear jurisdictional handling
The key issue is not whether misuse occurs.
It is that control becomes ambiguous.
You may not know:
- where the data is physically stored
- how long it persists
- whether it is isolated or duplicated
- how it is handled after processing
This creates a new category of legal risk:
secondary data exposure through processing systems.
The Irreversibility of Data Exposure in Legal Contexts
One of the most misunderstood aspects of digital risk in law is reversibility.
In many technical systems, mistakes can be corrected:
- files can be deleted
- access can be revoked
- systems can be patched
But legal consequences operate differently.
Once privileged information is exposed:
- it may be admissible
- it may be reviewed by opposing counsel
- it may influence the outcome of a case
And critically:
it cannot be “unseen.”
Courts do not evaluate intent in the same way systems do. They evaluate outcomes.
If protected information is disclosed—even unintentionally—the protection may be lost. This is the moment where technical convenience intersects with legal permanence.
Legal Ethics Have Not Changed—But the Environment Has
The professional responsibilities of legal practitioners remain consistent:
- protect client confidentiality
- maintain competence in tools and systems
- exercise reasonable care in handling information
What has changed is the environment in which those responsibilities operate.
Legal workflows have shifted from:
- paper-based, centralized control
to:
- distributed systems
- shared infrastructure
- external processing layers
This introduces complexity that did not previously exist. The responsibility, however, has not shifted. It still resides with the practitioner.
The Structural Misalignment Between Legal Risk and Modern Tools
The core issue is not user error. It is architectural misalignment.
Modern tools are designed for:
- speed
- accessibility
- collaboration
Legal systems require:
- containment
- traceability
- control
These priorities are not the same.
And when legal professionals rely on tools optimized for a different purpose, risk emerges—not from negligence, but from design.
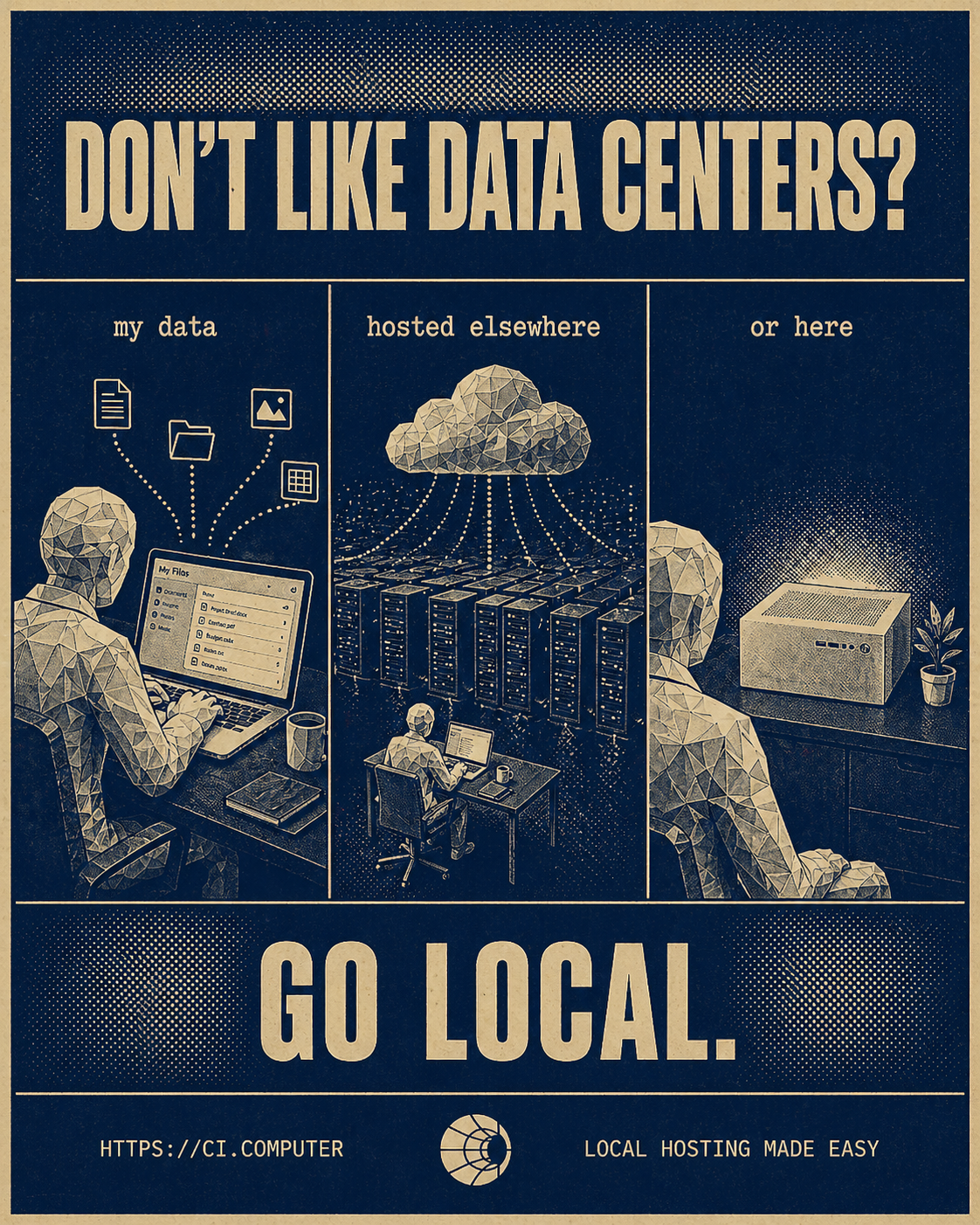
Rethinking Where Legal Data Lives
As legal workflows continue to incorporate cloud systems and AI tools, a more fundamental question becomes necessary:
Where does your data actually live—and where does it go after you use it?
This includes:
- storage location
- processing environment
- replication across systems
- long-term persistence
Access is not the same as control.
And in legal contexts, that distinction determines whether information remains protected.
A Shift Toward Contained, Controlled Data Environments
The emerging response to these risks is not to abandon technology—but to reconsider architecture.
This includes:
- limiting unnecessary data exposure
- reducing reliance on uncontrolled external systems
- maintaining clearer boundaries around sensitive information
- prioritizing environments where data handling is observable and controlled
The goal is not to eliminate convenience. It is to align tools with the realities of legal risk and generic tool adoption.
Final Thought
The systems most legal professionals rely on today are not inherently unsafe. But they are not neutral. These tools are built with general assumptions about how information should move.
And in legal work, movement itself can be the risk.
Because once information leaves your control, the question is no longer how it was handled—It is whether it remains protected at all.